Webinar 1: 9th June 1pm EEST, 10th June 2 PM EDT
How to build a next-gen SOC 45 mins

A security operations center (SOC) is the central location from which an organization defends itself against security breaches, data theft, and identity fraud. From within the SOC, security staff work continuously to keep adversaries at bay by bringing people, processes, and technology together.
However, in these times of sophisticated attacks, organizations need to step up and build a truly next-gen SOC. They need to build a SOC that is resilient, streamlined, responsive, intelligent, and automated. But how do they do this?
Join this webinar to learn how to build a next-gen SOC.
In this webinar, you’ll learn how to:
-
Fundamental responsibilities of a SOC.
-
The importance of the incident response feedback loop.
-
Building a next-gen SOC from the ground up.
-
Detection techniques such as cloud monitoring, anomaly detection, and correlation.
-
Response techniques such as alerting, workflows, and root cause analysis.
Register for this webinar
Webinar 2: 10th June 1pm EEST, 11th June 11am EDT
Most overlooked areas in organizations’ IAM strategies 45 mins

Why attend this webinar?
Managing IT users and resources requires constant vigilance. It takes only one weak link in your IT management process for a cybersecurity incident to happen. To lower the chances of making the news for the wrong reasons, review the neglected areas of your organization’s IAM approach.
In this webinar, you’ll learn how to:
-
Reliance on manual processes
-
Ease of administration for IT staff
-
Privileged user management
-
Access management practices
-
Reports and real-time alerts
Register for this webinar
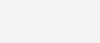
Webinar 3: 16th June 1pm EEST, 17th June 2pm EDT
Security analytics: 5 anomalies to watch out for in your network 45 mins
Why attend this webinar?
Unusual events occur in a network that is under attack. These events, called anomalies, can be tracked by security teams to identify and investigate potential security threats at an early stage. Modern day security information and event management (SIEM) solutions come with user and entity behavior analytics (UEBA) to help security teams do just that.
So, what are the anomalies you need to watch out for, and how do you analyze your logs to spot these anomalies? Join our webinar to get started with monitoring your network for anomalous security events.
By attending this webinar, you’ll learn how to:
-
How to augment SIEM with UEBA
-
How to audit anomalies and risk scores of users
-
Five anomalies to track in your network
-
Use cases for SIEM and UEBA
Register for this webinar
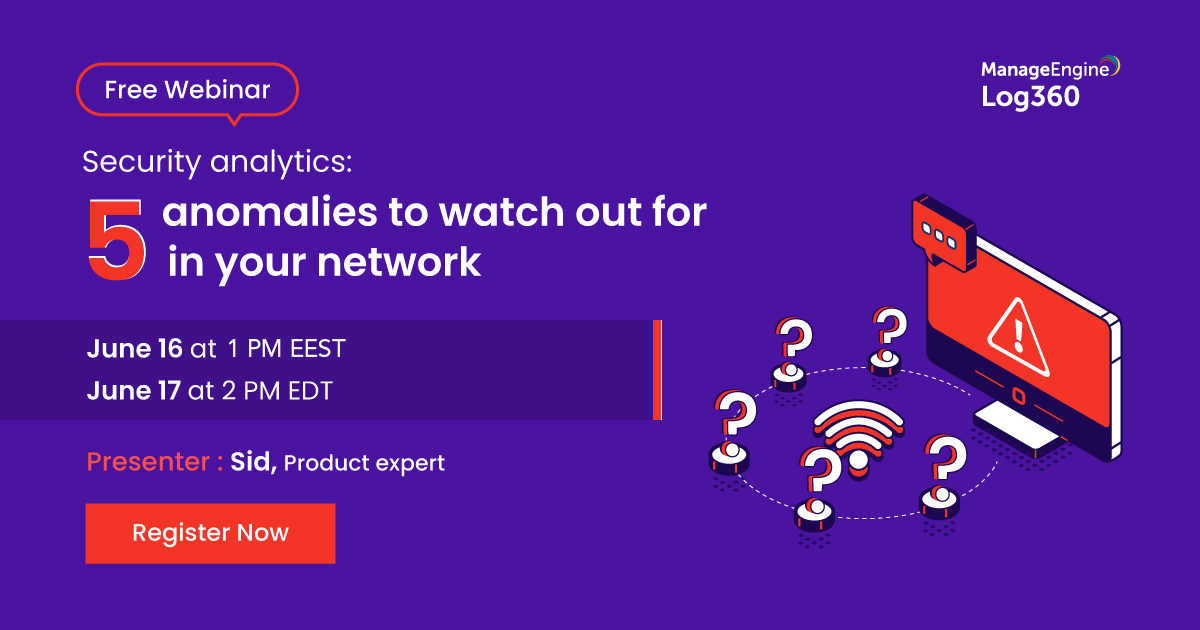
Webinar 4: 17th June 5pm EEST
Password security in the time of remote work 45 mins
Why attend this webinar?
With the global outbreak of COVID-19, more organizations are adapting to work-from-home. This webinar will cover a few tips and tricks for a seamless password self-service experience for your remote users.
We will cover:
-
Password reset for remote employees
-
Password expiration notification for remote users
-
Web-based password changes for Active Directory
-
Tips for better password security
Register for this webinar
Webinar 5: 18th June 5pm EEST
PowerShell as a cyberattack tool 45 mins
PowerShell is a powerful command-line tool that comes built in with most Windows systems. Up until now, it has been a useful tool for administrators to automate tedious tasks; now, however, it has been weaponized and is being used to carry out cyberattacks.
We will cover:
-
How malicious actors leverage PowerShell in attacks
-
How to detect the telltale signs of a PowerShell attack
-
How to configure alerts about malicious PowerShell use, and take immediate remedial action
Register for this webinar
Webinar 6: 24th May 1pm EEST, 25th June 2pm EDT
Choosing the right enterprise IAM strategy for Active Directory and Azure Active Directory 45 mins

Why attend this webinar?
Do the right people have the right access to resources? What are the users doing with their access? Are there sufficient methods to control access? Whether your environment is a cloudless ecosystem, in the cloud, or a hybrid of both, it’s crucial to choose the right identity and access governance approach.
In this webinar, you’ll learn to:
-
Learn about various identity and access management (IAM) strategies offered by Active Directory (AD) and Azure AD.
-
Determine possible limitations of IAM approaches in AD and Azure AD.
-
Choose the right IAM strategy for on-premises, cloud, and hybrid deployments with AD360.
Register for this webinar
Alternatively you may call the number +35722256811 in Cyprus and in Greece +302109340288 for more information.